Agents do what you mean.
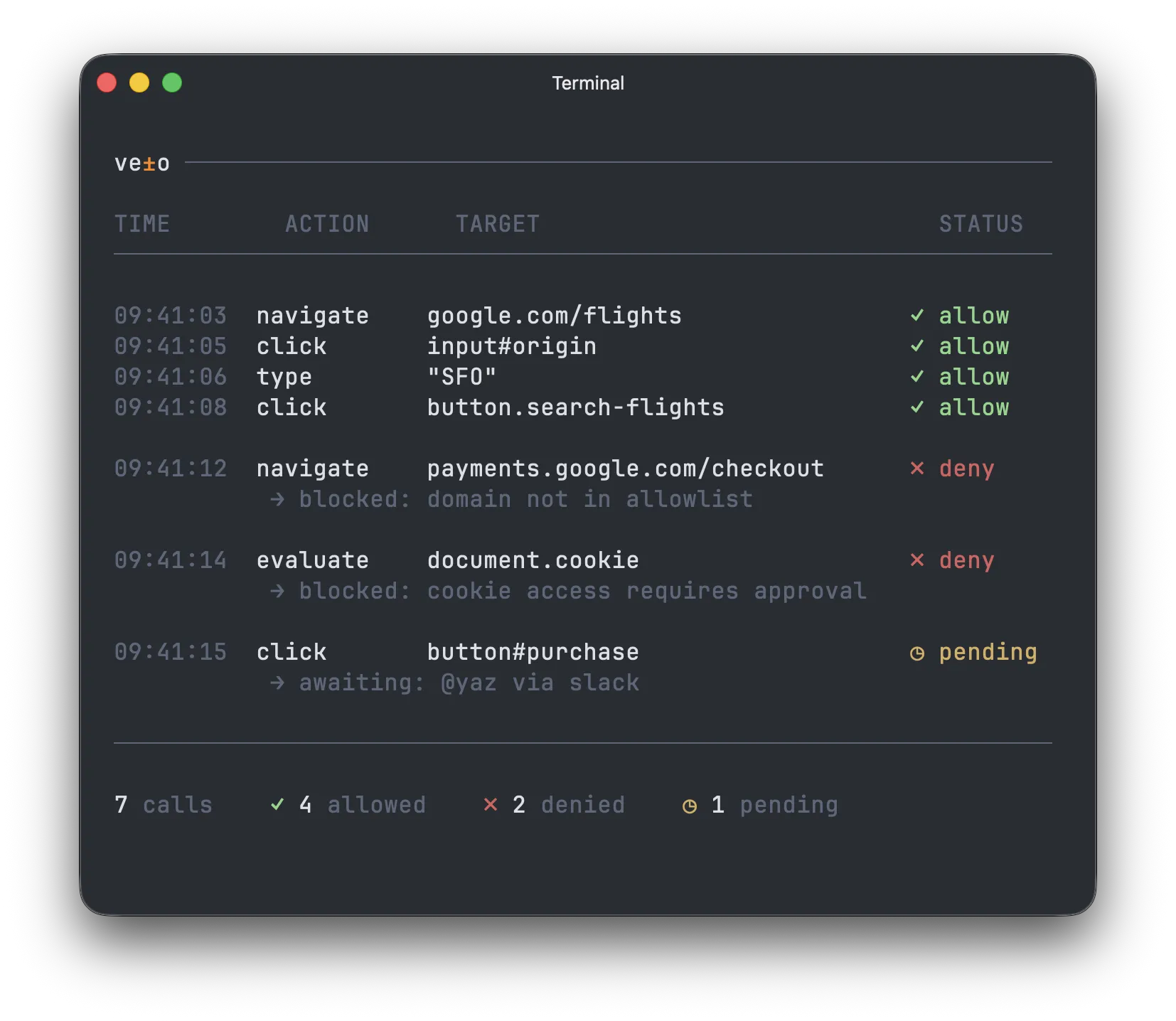
Veto turns your intent into enforceable permissions for every agent action — before it touches money, data, or prod.
Apache 2.0·<5ms local eval·TypeScript + Python·Works with OpenAI, Anthropic, LangGraph, CrewAI, MCP+
The shift
Agents are getting more capable. Authority should too.
Three calls to issue_refund. Three different authorities. Veto reads the difference.
Routine, high-value, and flagged accounts — each one matched to the rule you wrote.
Integration
Two lines of code. Every call, on the record.
Import the SDK. Wrap your tools. Policies are in English, version-controlled, and evaluated locally.
import OpenAI from 'openai'+import { protect } from 'veto-sdk' const openai = new OpenAI() +const tools = await protect([ { type: 'function', function: { name: 'issue_refund', parameters: { type: 'object', properties: { amount: { type: 'number' }, customer_tier: { type: 'string' }, }, }, }, }, ]) // Everything else stays the same await openai.chat.completions.create({ model: 'gpt-5.4', tools, messages })The veto link is a handshake.
When your agent reaches the edge of its authority, it doesn't stop — it asks. The person on the other end sees the exact call, the policy that caught it, and a one-click path forward. Agents keep moving. Humans stay in the loop on what matters.
Capabilities4 primitives
Core primitives
Everything evaluates locally. No network calls in the enforcement path.
Policies in English
Write the rule the way you'd explain it to a new hire. Veto compiles to a deterministic IR.
Local-first engine
Every call evaluated in your process. <5ms median. No network hop on the happy path.
Veto links
High-stakes calls route to the right human. Slack, email, dashboard — signed and logged.
Circuit breakers
Auto-halt agents when error or spend thresholds are crossed. Fails closed, not silent — every trip is logged and signed.
Spend-aware rulesNew
Budgets with cost extraction across x402, Stripe, and AP2.
Every call, on the record
OpenTelemetry spans, signed decisions, versioned policy history. Export anywhere.
Output review
Inspect and redact what the agent returns, with the same policy language.
Tied to a name
Every decision traced to agent, user, and policy version.
Why Veto
The authority layer — separate from identity, separate from the prompt.
Identity says who. Prompts say what. Veto says how far — deterministically, at runtime.
Integrations
Every major agent framework. Day one.
Veto wraps tools, not frameworks. If your system calls tools, Veto can govern them. See all integrations
Plans
Pricing
Start building for free. Scale when you ship. The SDK is free forever, and Veto Cloud adds the dashboard, approvals, audit retention, and compliance exports.
Free
Hosted governance for early projects. No card required.
- Plain-English policy compiler and hosted dashboard
- Signed tamper-evident audit chain
- HITL links via email
- All 12 framework integrations
- Bring your own LLM key for unlimited compiles
Pro
Production teams running tool-calling agents as first-class infrastructure.
$99/mobilled annually
- RBAC, webhooks, Slack + SMS HITL delivery
- Full audit log export and SIEM streaming
- Policy version history and time-travel diffs
- Bring your own LLM key to uncap compiles
- SSO on request
Over the cap: $0.50 / 1K decisions · $0.02 / compile · BYOK zeros the compile line
Scale
Multi-tenant AI products and high-volume deployments.
$999/mobilled annually
- Bring your own cloud (BYOC) deployment
- Per-tenant policy scoping for multi-tenant SaaS
- White-label HITL approval flows with your branding
- Multi-region data residency
- Bring your own LLM key to uncap compiles
- SSO (SAML/OIDC) and SCIM provisioning
Over the cap: $0.30 / 1K decisions · $0.015 / compile · BYOK zeros the compile line
Enterprise
Regulated deployments with contract controls, on-prem parity, and customer-owned audit boundaries.
- Dedicated infrastructure and custom deployment topologies
- Uptime SLA with penalty clauses
- HIPAA BAA, EU DPA, and vendor questionnaire support
- Customer-owned audit chain on on-prem
- BYOK by default — route compiles through your own Bedrock, Azure OpenAI, or Vertex endpoint
- Dedicated Slack channel and named CSM
Common questions
Questions developers ask
You can — until you have 40 tools across 6 agents with per-tenant rules, temporal constraints, budget caps, and an auditor asking for proof. Veto gives you a single declarative layer that handles all of that, versioned in YAML, enforced at runtime, with a full decision log. The alternative is reimplementing an authorization engine inside every agent you ship.
Nothing. The SDK evaluates policies locally, in-process. There is no network call in the enforcement path. Cloud features — the dashboard, approval queue, audit retention — degrade gracefully. Your agent never stalls waiting for Veto.
Under 5ms. Policy evaluation is deterministic and runs in the same process as your agent. For comparison, the average LLM tool-call round trip is 500–2,000ms. Veto is noise.
Veto wraps tools, not frameworks. OpenAI, Anthropic, LangChain, CrewAI, Vercel AI, PydanticAI, MCP, browser agents — if your agent calls tools, Veto can govern them. One import and one function call, no architecture changes.
The SDK is Apache-2.0. You can read every line, fork it, self-host it, and never pay us. Veto Cloud is paid — it adds the dashboard, team approvals, analytics, and managed audit retention. The enforcement engine that makes the allow/deny decision is fully open and always will be.
Proof of control, proof of oversight, proof of record — that is what every compliance framework boils down to. Veto produces all three as a side effect of doing authorization. Policy enforcement is the control. Approval gates are the oversight. The decision log is the record. Same evidence, different cover sheet — EU AI Act, SOC 2, HIPAA, take your pick. Need the full path to certification? We partner with compliance automation platforms and get you there.
Your agent can call any tool it has access to — issue a refund, delete a record, send an email to every customer on your list. "Can" just means the tool exists. "May" is whether policy says yes. Most agent frameworks never check permission. The model decides to call a tool and the tool executes. Veto sits between the decision and the execution.
Open source
Every platform gets its trust layer.
Apache-2.0. TypeScript and Python. Ship it today.
